Please fill in this little feedback survey, 2 minutes of your time, great help for us !
NAXSI means Nginx Anti XSS & SQL Injection.
Technically, it is a third party nginx module, available as a package for
many UNIX-like platforms. This module, by default, reads a small subset of
simple (and readable) rules
containing 99% of known patterns involved in
website vulnerabilities. For example, <, | or drop are not supposed
to be part of a URI.
Being very simple, those patterns may match legitimate queries, it is the Naxsi's administrator duty to add specific rules that will whitelist legitimate behaviours. The administrator can either add whitelists manually by analyzing nginx's error log, or (recommended) start the project with an intensive auto-learning phase that will automatically generate whitelisting rules regarding a website's behaviour.
In short, Naxsi behaves like a DROP-by-default firewall, the only task is to add required ACCEPT rules for the target website to work properly.
Contrary to most Web Application Firewalls, Naxsi doesn't rely on a signature base like an antivirus, and thus cannot be circumvented by an "unknown" attack pattern. Another main difference between Naxsi and other WAFs, Naxsi filters only GET and POST requests, is Free software (as in freedom) and free (as in free beer) to use.
Naxsi is compatible with any nginx version, although it currently doesn't play well with the new HTTPv2 protocol added in recent nginx versions. See issue #227 for more details.
It depends on libpcre for its regexp support, and is reported to work great on NetBSD, FreeBSD, OpenBSD, Debian, Ubuntu and CentOS.
- The documentation
- Some rules for mainstream software
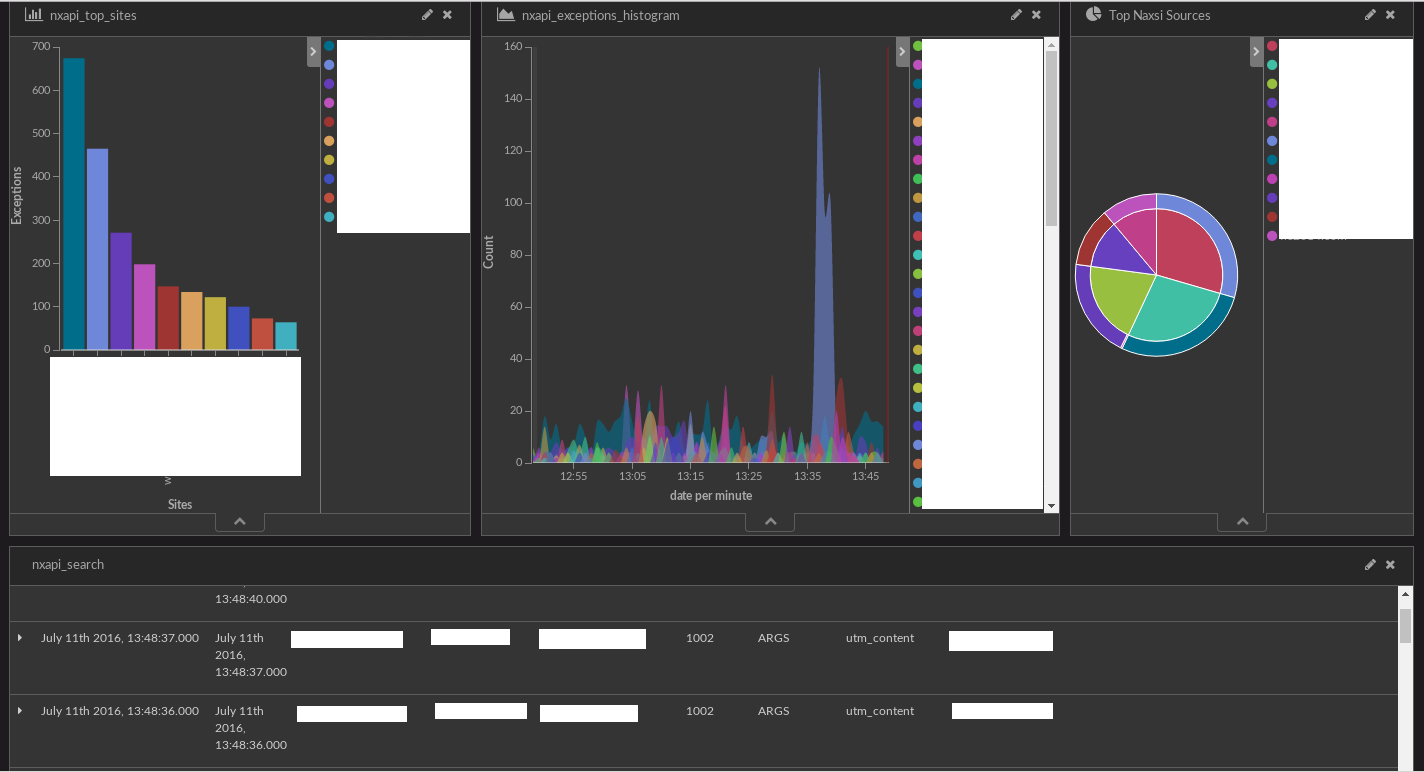
- The nxapi/nxtool to generate rules
If you find a security issue, please send it by email to [email protected];
you can use the gpg key
0x251A28DE2685AED4
to encrypt it.